Setup Wireguard VPN for Mobile Clients
Wireguard is a modern, sleek, VPN that promises to be super easy to install and setup, as well as being faster than IPSec. With pretty much a client for every device, it’s a great option for running on a home or office network VPN. This guide outlines how to setup and configure the VPN server and mobile (Android, but iOS should be the same) client.
#get the interface ip address
#escalate privilege sudo su
#install wireguard + tools apt update apt install wireguard wireguard-tools qrencode
#generate keys wg genkey | tee /etc/wireguard/server_private.key | wg pubkey | tee /etc/wireguard/server_public.key wg genkey | tee /etc/wireguard/android-private.key | wg pubkey > /etc/wireguard/android-public.key
#create server configuration file nano /etc/wireguard/wg0.conf [Interface] # Set the IP range that client devices will receive an IP in Address = 10.220.0.1/24 Address = fd86:ea04:1115::1/64 # The port that will be used to listen to connections. 51820 is the default. ListenPort = 51820 # server's private key. PrivateKey = VPN_SERVER_PRIVATE_KEY PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE; ip6tables -A FORWARD -i %i -j ACCEPT; ip6tables -t nat -A POSTROUTING -o eth0 -j MASQUERADE; PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE; ip6tables -D FORWARD -i %i -j ACCEPT; ip6tables -t nat -D POSTROUTING -o eth0 -j MASQUERADE [Peer] #android phone PublicKey = MOBILE_PUBLIC_KEY # The IP address that will be assigned to this client AllowedIPs = 10.220.0.2/32, fd86:ea04:1115::2/128
#secure the wireguard folder chown -R root:root /etc/wireguard/ chmod -R og-rwx /etc/wireguard/*
#enable ip forwarding nano /etc/sysctl.conf #add to end of file net.ipv4.ip_forward = 1 net.ipv6.conf.all.forwarding=1 sysctl -p
#wireguard service commands systemctl enable wg-quick@wg0.service systemctl start wg-quick@wg0.service systemctl stop wg-quick@wg0.service
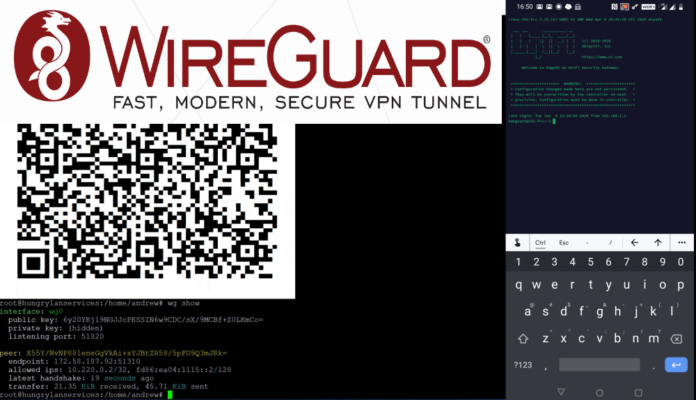
#wireguard status wg show
#create client configuration file nano /etc/wireguard/android.conf [Interface] PrivateKey = MOBILE_PRIVATE_KEY Address = 10.220.0.2/32, fd86:ea04:1115::2/128 DNS = 9.9.9.9 [Peer] PublicKey = VPN_SERVER_PUBLIC_KEY Endpoint = publicipaddressofwireguardserver:51820 AllowedIPs = 0.0.0.0/0, ::/0
#generate the QR code qrencode -t ansiutf8 < /etc/wireguard/android.conf